Prepare your enterprise to conduct individualized self-assessments of risk, so you can make realistic decisions on how to avoid cyber threats. The 2015 DBIR expands its investigation into nine common threat patterns and sizes up the effects of all types of data breaches, from small data disclosures to events that hit the headlines.
Welcome (and welcome back), friends, to our annual showcase of security breaches. We’re so glad you could attend; come inside, come inside. The year 2014 saw the term “data breach” become part of the broader public vernacular with The New York Times devoting more than 700 articles related to data breaches, versus fewer than 125 the previous year. 2 It was the year major vulnerabilities received logos (collect them all!) and needed PR IR firms to manage their legions of “fans.” And it was the year when so many high-profile organizations met with the nigh inevitability of “the breach” that “cyber” was front and center at the boardroom level. The real sign of the times, however, was that our moms started asking, “Is that what you do, dear?” and seemed to finally get what we do for a living.
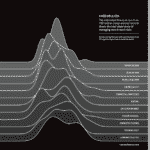
The 2015 Data Breach Investigations Report (DBIR) continues the tradition of change with additions that we hope will help paint the clearest picture yet of the threats, vulnerabilities, and actions that lead to security incidents, as well as how they impact organizations suffering them. In the new “Before and Beyond the Breach” section, our security data scientists analyzed
(literally) dozens of terabytes of data from partners new and old, making this one of the most collaborative, data-driven information security (InfoSec) reports in existence. If you’re accustomed to reading the DBIR mainly for the headliners and one-liners, you might need to coffee up and put your thinking cap on for this one. But it’ll be worth it; we promise. Fret not, “incident pattern” aficionados—the nefarious nine are back, but they have slimmed down a bit, as you’ll see when you get to that section.